The craft of creating a replica of a locking mechanism’s access tool is an ancient art, dating back to the time when the first locks were invented. This practice, essential for granting entry to multiple individuals or ensuring access in case of a lost original, involves precision and skill.
In 2024, the artistry has evolved, combining traditional locksmith techniques with advanced technological solutions, ensuring that the integrity of the original is maintained while producing a functional counterpart.
The Science Behind Key Replication
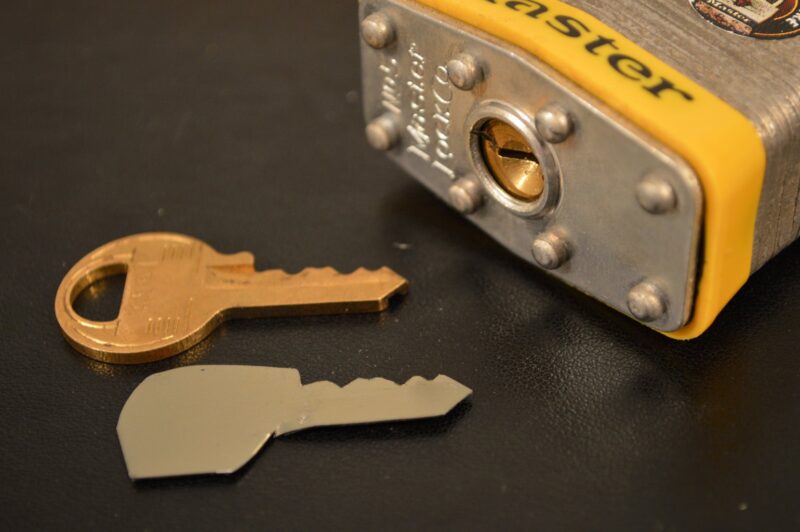
Key replication is not just an art; it’s also a science. It involves understanding the unique pattern of notches, grooves, or indentations that make each original unique. Professionals in the field use this knowledge, along with sophisticated machinery, to create an exact match.
Modern replication processes often involve digital imaging and cutting technology, ensuring a precision that was not possible in earlier times.
Understanding Key Types and Their Duplicability

Various types of locking mechanisms require different approaches for replication. From the traditional pin-tumbler models to more complex magnetic or electronic systems, each comes with its own set of challenges.
While most traditional designs can be duplicated easily, high-security models often have patented designs or require specialized equipment and authorization for replication, ensuring an additional layer of security.
Traditional Key Duplication Methods
Traditional duplication methods involve manually adjusting a blank to match the original’s teeth and grooves using a machine called a duplicator. The locksmith carefully aligns both the original and the blank against the machine’s guides before tracing the original’s pattern onto the blank.
Despite the advent of modern technology, this manual craftsmanship remains popular for its precision and reliability.
The tactile feedback and hands-on approach provide a level of detail that machines can’t always replicate, making it ideal for older or unique lock types where a personalized touch is essential. To learn more about the process of duplication you should check here.
Modern Key Duplication Technologies
Advancements in technology have introduced methods like laser cutting and code cutting. Laser cutting uses a high-powered laser to precisely cut the pattern into the blank, often used for more complex or high-security designs.
Code cutting, on the other hand, involves inputting the lock’s unique code into a machine, which then automatically produces the design without needing the original as a guide.
These methods significantly reduce the risk of human error, ensuring a high degree of accuracy and providing a quick solution for bulk duplication needs in commercial settings.
Professional Key Duplication Services
Professional locksmiths offer skilled services, ensuring a high-quality replica. These experts not only have access to advanced cutting machinery but also possess the knowledge and experience to handle a wide range of lock types.
Their services provide a reliable solution for those needing a duplicate, especially for designs that require a high level of precision or authorization.
In addition to technical expertise, professional locksmiths also offer valuable advice on maintaining security and can provide solutions for locks that are damaged or worn out.
DIY Key Duplication Risks and Benefits

While do-it-yourself kits are available, they come with risks. The precision of a professionally cut duplicate is hard to achieve with a DIY approach, leading to potential damage to the lock or ineffective replicas.
However, for less complex and non-security-critical situations, DIY duplication can be a cost-effective and immediate solution.
These kits are particularly useful for everyday, low-risk applications, such as duplicating keys for interior doors or simple padlocks, where precision is not as critical.
Legal and Ethical Aspects of Key Duplication
Duplicating certain types of locking mechanisms, especially those classified as high-security, may require proof of ownership or authorization. This legal framework ensures that the replication process does not become a tool for unauthorized access.
Ethically, it’s crucial to respect the privacy and security of others by only duplicating your own or with explicit permission from the owner. Responsible duplication practices ensure that the security of the lock is not compromised and that trust in locksmith services is maintained.
Key Duplication for Security and Convenience
While the primary purpose is often to provide convenient access to multiple users or serve as a backup, it also plays a role in security. Property managers, for instance, rely on this process to ensure access to their premises in emergencies.
However, it’s crucial to manage and track duplicates to prevent unauthorized access, maintaining a balance between convenience and security.
Effective management of duplicates includes implementing strict check-out procedures and regular audits to ensure that all copies are accounted for and in the right hands.
Limitations and Challenges of Key Replication
Despite advancements, duplication is not always straightforward. High-security models often come with features designed to thwart duplication, like special codes, magnetic components, or complex patterns.
Additionally, wear and tear on the original can make accurate duplication challenging, requiring expert assessment and sometimes even reconstruction of the original pattern.
This makes the expertise of a seasoned locksmith invaluable, especially when dealing with antique or highly secure locking mechanisms that demand a nuanced approach.
Tips to Protect Your Locking Mechanisms from Unauthorized Duplication

To safeguard against unauthorized replication, consider using high-security models with patented designs or restricted duplication rights.
Regularly changing codes for electronic systems and maintaining control over who has access to originals are also effective strategies.
For businesses, maintaining a log of who holds duplicates and regularly auditing this can help in tracking and managing access. Additionally, using non-duplicable key designs or integrating additional security measures like biometric locks can significantly enhance overall security.
Future Trends in Duplication: What to Expect in 2024
The future of duplication is likely to involve further integration of digital technology. Biometric systems, advanced encryption for electronic models, and even blockchain technology for tracking and authorization are on the horizon.
These advancements aim to offer enhanced security, making unauthorized duplication even more challenging and giving owners more control and insight into who has access to their spaces.
The trend is moving towards personalized, user-specific access solutions, reducing the reliance on physical duplicates and shifting the focus to digital management and advanced security protocols.
Conclusion
In conclusion, while the duplication of locking mechanisms is a complex field with a rich history, it’s clear that the blend of traditional craftsmanship, modern technology, and legal frameworks provides a multifaceted approach to managing access.
Whether for convenience, security, or emergency preparedness, understanding the nuances of this craft is crucial for anyone looking to navigate the intricacies of duplicating these crucial tools of access and security.
Related Posts:
- Top 10 Things To See and Do in Egypt Before You Die…
- What is the Best Way to Explore Egypt? Tips for…
- Peloton Yoga Basics and Crucial Tips for New Yoga…
- Computer Turns on but Monitor Says No Signal - 9 Ways to Fix
- From Security to Productivity: Common Use Cases of…
- Tips on How to Turn a Photo into a Paint by Number…